How Legacy System Modernisation Improves Cybersecurity?
Technology evolves fast. Cyber threats evolve even faster.
Yet many businesses still rely on outdated systems built years sometimes decades ago. While those systems may still “work,” they often create hidden security risks that companies don’t notice until it’s too late.
A single outdated server, unsupported application, or weak authentication process can become an easy entry point for cybercriminals.
That’s why legacy system modernisation is no longer just an IT upgrade. It has become a critical cybersecurity strategy.
Modern businesses need secure, scalable, and resilient systems capable of defending against ransomware, data breaches, phishing attacks, and evolving cyber threats. Companies that continue relying on aging infrastructure risk operational downtime, financial losses, and damaged customer trust.
In this guide, we’ll explain how legacy software modernization improves security, reduces vulnerabilities, and helps businesses stay competitive in a digital-first world.
What Is Legacy System Modernisation?
Legacy system modernisation refers to upgrading outdated software, applications, infrastructure, or business systems to modern technologies that offer better performance, scalability, and security.
This process may include:
- Migrating systems to the cloud
- Replacing unsupported software
- Refactoring legacy applications
- Improving infrastructure architecture
- Integrating modern cybersecurity tools
- Updating databases and APIs
The goal is not just to “refresh” technology. It is to make systems safer, faster, and future-ready.
Understanding Legacy Systems:
Legacy systems are older technologies still used by businesses despite being outdated or unsupported.
Common examples include:
- Old ERP platforms
- Unsupported Windows servers
- Monolithic applications
- Legacy databases
- Older authentication systems
Many organizations continue using them because replacing them feels expensive or risky. However, delaying modernization often creates much bigger costs later.
Also Read: Affordable Financial Institution Cybersecurity Audit Service
Why Legacy Systems Create Major Cybersecurity Risks?
Older systems were not designed for today’s threat landscape.
Modern cyberattacks are more sophisticated, automated, and aggressive than ever before. Unfortunately, outdated infrastructure struggles to defend against them.
Unsupported Software and Missing Security Patches:
One of the biggest dangers of outdated systems is the lack of vendor support.
When software reaches end-of-life status, security patches stop arriving. That means vulnerabilities remain exposed permanently.
Hackers actively target unsupported systems because they know weaknesses remain unpatched.
According to IBM, the average global cost of a data breach reached millions of dollars in recent years, with outdated infrastructure being one of the contributing factors.
Weak Authentication Systems:
Many older platforms lack:
- Multi-factor authentication (MFA)
- Biometric security
- Role-based access controls
- Zero-trust security support
Weak login systems increase the risk of unauthorized access and insider threats.
This is where legacy system cybersecurity becomes a serious concern.
Outdated Software Vulnerabilities Are a Growing Business Threat:
Cybercriminals specifically look for businesses using old technologies.
Why?
Because outdated software vulnerabilities are easier to exploit.
Older applications often rely on:
- Weak encryption protocols
- Insecure APIs
- Deprecated coding frameworks
- Poor access control systems
These weaknesses increase exposure to:
- Ransomware attacks
- Malware infections
- Data theft
- System hijacking
- Compliance violations
Common Risks Found in Legacy Systems:
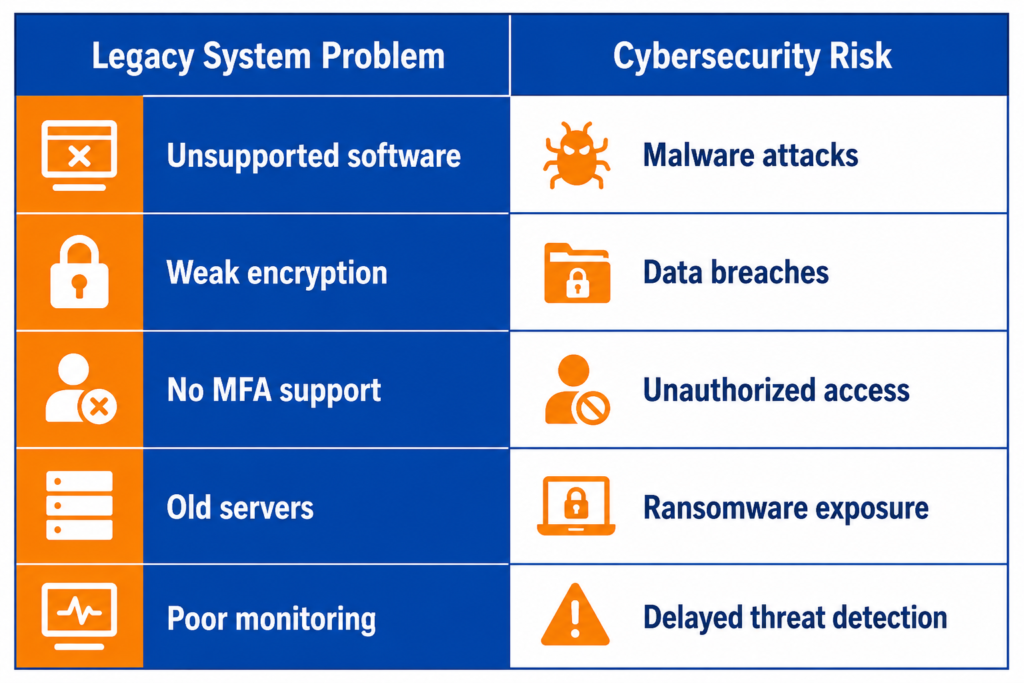
A system may still function operationally while silently becoming a security liability.
How Legacy System Modernisation Improves Cybersecurity?
Modernization dramatically strengthens business security.
It helps organizations move away from vulnerable technologies and adopt modern security-first infrastructures.
Better Security Patch Management:
Modern systems receive regular security updates.
This reduces exposure to known vulnerabilities and helps businesses stay protected against emerging cyber threats.
Automatic patching also minimizes human error and improves operational efficiency.
Stronger Data Encryption:
Modern platforms use advanced encryption protocols to secure sensitive information both in storage and during transmission.
This significantly improves legacy application security and reduces the risk of stolen customer or financial data.
Improved Identity and Access Management:
Modernized systems support:
- Multi-factor authentication
- Role-based permissions
- Identity verification tools
- Zero-trust architecture
These features reduce unauthorized access risks and improve compliance readiness.
AI-Powered Threat Monitoring:
Modern cybersecurity solutions can detect suspicious activity in real time.
AI-driven monitoring tools help businesses identify:
- Unusual login behavior
- Malware activity
- Data exfiltration attempts
- Internal security threats
Older systems rarely support this level of intelligent monitoring.
Secure Cloud Infrastructure:
Cloud-based environments often include:
- Automated backups
- Disaster recovery systems
- Continuous monitoring
- Built-in compliance tools
This makes cybersecurity modernization significantly more effective than maintaining outdated on-premise infrastructure.
Legacy Application Modernization Supports Digital Transformation:
Security is no longer separate from business growth.
Companies investing in legacy application modernization often improve:
- Productivity
- Scalability
- Customer experience
- Operational efficiency
- Regulatory compliance
Modernization also strengthens digital transformation cybersecurity, ensuring businesses can innovate without increasing risk exposure.
Signs Your Legacy Systems Are Becoming Security Risks:
Not every outdated system immediately fails.
But there are warning signs businesses should never ignore.
Frequent Downtime:
If systems crash regularly or become unstable, infrastructure weaknesses may already exist.
Increasing Maintenance Costs:
Many organizations spend huge amounts maintaining outdated technology rather than upgrading it.
Over time, maintenance becomes more expensive than modernization itself.
Slow Performance and Integration Issues:
Legacy systems often struggle to integrate with modern tools and cloud services.
This limits agility and increases operational inefficiencies.
Compliance Challenges:
Regulations around data privacy and cybersecurity continue becoming stricter.
Older systems may fail to meet standards such as:
- GDPR
- HIPAA
- PCI DSS
Compliance failures can lead to heavy penalties and reputational damage.
Cloud Migration vs Full System Replacement:
Not every business requires a complete rebuild.
Sometimes cloud migration alone can significantly improve security.
When Cloud Migration Makes Sense?
Cloud migration works well when:
- Core applications remain usable
- Businesses need better scalability
- Security upgrades are the main priority
- Infrastructure costs need reduction
When Full Modernization Is Necessary?
Complete modernization may be necessary when:
- Systems are unsupported
- Software architecture is obsolete
- Performance issues are severe
- Security risks are critical
| Approach | Security Improvement | Cost | Complexity |
| Cloud Migration | Moderate to High | Moderate | Moderate |
| Full Rebuild | Very High | High | High |
The right strategy depends on business goals, risk exposure, and long-term scalability needs.
Cybersecurity Modernization Is Becoming a Competitive Advantage:
Customers care about security more than ever.
Businesses handling sensitive customer information must demonstrate trust, reliability, and resilience.
Companies with modern infrastructures benefit from:
- Stronger customer confidence
- Faster recovery from incidents
- Better scalability
- Lower operational risks
- Improved business continuity
Cybersecurity is no longer just an IT responsibility. It directly affects reputation, growth, and customer loyalty.
Future Cybersecurity Trends Driving Modernisation:
Several trends are accelerating the need for modernization.
Zero Trust Security:
Organizations are moving toward “never trust, always verify” security models.
AI-Driven Security Automation:
AI tools are helping businesses detect and respond to threats faster than traditional methods.
Secure Multi-Cloud Infrastructure:
Businesses increasingly rely on multi-cloud environments for flexibility and resilience.
Compliance-First Architecture:
Modern applications are now built with security and compliance integrated from the beginning.
These trends make legacy software modernization essential for long-term competitiveness.
Final Thoughts:
The biggest cybersecurity risk is not always the hacker.
Sometimes it’s the outdated system quietly running in the background.
As cyber threats continue evolving, businesses can no longer rely on aging infrastructure that lacks modern security protections. Legacy system modernisation helps organizations reduce vulnerabilities, improve operational resilience, and prepare for future growth.
Modernization is not simply about replacing old software. It is about protecting business continuity, customer trust, and long-term success.
Businesses that modernize early gain a major advantage in security, scalability, and digital transformation readiness.
If your organization is struggling with outdated infrastructure, unsupported systems, or growing security concerns, Marsmatics can help businesses modernize legacy applications with scalable, secure, and future-ready technology solutions.
FAQs
What is legacy system modernisation?
Legacy system modernisation is the process of upgrading outdated software, infrastructure, or applications to improve security, performance, scalability, and compatibility with modern technologies.
Why are legacy systems vulnerable to cyberattacks?
Legacy systems often lack modern security updates, advanced encryption, MFA support, and real-time threat monitoring capabilities, making them easier targets for cybercriminals.
Does cloud migration improve cybersecurity?
Yes. Cloud platforms typically provide stronger security controls, automated backups, continuous monitoring, and faster patch management compared to traditional legacy infrastructure.
When should businesses modernize legacy systems?
Businesses should consider modernization when systems become expensive to maintain, unsupported, difficult to scale, slow, or increasingly vulnerable to cybersecurity threats.